Friends, Its time to write something for FBA in SP2010 now. I hope you knows how to configure FBA in MOSS 2007. If not aware of it, Please read my previous article on FBA in MOSS 2007
There are minor differences with configuring FBA for SP2010 compared to MOSS 2007. Like, SP2010 does not support classic FBA, relatively FBA is provided through Claims Authentication. Moreover, introduced SSS (Secure Store Service) which is the next-gen of SSO (Single Sing On) services.
Forms Based Authentication in ASP.NET leverages a provider model. You can leverage the out of box providers like the “SqlMembershipProvider” as I will in this post. Alternatively, you can build your own providers as detailed in the MSDN topic. This means you could use any data store, not just SQL Server. You could use an XML file if you so choose, or you can use an LDAP server, or another database like Oracle or MySQL.
Microsoft ships providers that work with a SQL Server database. The scripts to create the database are located at:
C:\Windows\Microsoft.NET\Framework\v2.0.50727
It is better to use a tool called “aspnet_regsql” rather than run the scripts individually that can be used to configure a database to use ASP.NET application services. If you have done this in MOSS 2007, you will see that there are a few new steps here and there, but overall things are pretty simple once you configure everything.
Goal
Configure a web application for Claims based authentication using SQL Membership Providers. Store membership credentials in a SQL database.
Before configuring FBA in SP2010, question should come in your mind What are the differences between Classic Mode Authentication and Claims based Authentication?. Let me explain you this before configuring FBA in SP2010.
SharePoint 2010 you can create web applications using Classic Based Authentication or Claims based Authentication. However, FBA can only be configured with web applications created using Claims Based Authentication.
Classic Mode Authentication: It refers to the integrated windows authentication. You cannot configure the Forms based authentication if your web application is using Classic Mode Authentication. You can convert a web application from Classic Mode Authentication to Claims Based Authentication. However, that can only be done using PowerShell commands and it is an irreversible process. I will explain in next article how to convert the web application from Classic Mode authentication to Claims Based Authentication.
Claims Based Authentication: SharePoint 2010 is built on Windows Identity Foundation. It enables authentication from windows as well as non-windows based systems. This also provides the capability to have multiple authentications in a single URL.
Game Plan:
STEP-1: Create a New SharePoint Application
STEP-2: Create the database using aspnet_regsql
STEP-3: Add users and roles using the Web Site Administration Tool
STEP-4: Add connection strings in the web.config for:
- Your application
- Central Administration
- Secure Token Service Application
STEP-5: Add membership and role providers for:
- Your application
- Central Administration
- Secure Token Service Application
STEP-6: Edit web.config for Central Administration
- Set the default provider for roles as AspNetWindowsTokenRoleProvider
- Set the default provider for membership as your new membership provider
- Add the PeoplePickerWildcards entry
STEP-7: Edit web.config for the Secure Token Service Application
- Set the default provider for roles as your provider
- Set the default provider for membership as your provider
STEP-8: Add the FBA administration user to Central Administration
STEP-9: Add FBA users to SharePoint groups
STEP-1: Create a New SharePoint Application
To create a new application open Central Administration and click the “Manage web applications” link under “Application Management” group. It will open another screen, click the ribbon toolbar button to create a new web application. That will pop open a modal window. In that dialog, choose “Claims Based Authentication” for the Authentication type. By default, SharePoint will create a new IIS web site for you. You can leave the default, or you can rename it. I accepted the default of “11574”.
Scroll down a bit, and configure the forms based authentication settings. Check the “Enable Forms Based Authentication” box, and configure the membership provider name as “FBAMembership” and the role provider name as “FBARoles”.
I have changed the identify of the application pool to Network Service.
NOTE: Here, i am not sharing all screen as it is very easy to create new application.
Scroll to the bottom and click OK, and SharePoint will agitate for a moment to create a new application for you.
Since you are using Windows authentication in addition to Forms Based Authentication, it is OK to click the link to create the site collection.
I created a new Team site called “FBA Demo”, specifying a Windows account as the primary administrator.
STEP-2: Create the database using aspnet_regsql
We have now created a new application, a site collection, and a top-level site. The next step is to configure the new application to use FBA.
Create the Database:
Open the Visual Studio 2010 Command Prompt from the start menu and type “aspnet_regsql”. This will open a new application that lets you create and configure a SQL Server database to use ASP.NET application services. I accepted all defaults and it created a new database called “aspnetdb” with the following table structure.

Now its time to add some users to the database to test our solution. The easiest way to do this is by leveraging Visual Studio.
Create a new project in Visual Studio 2010 using the “ASP.NET Empty Web Site” project template. Edit the web.config file. There is an empty element, “” that you will edit as below:
Now the next step is to configure a Membership and Role provider. Right above the end tag, add the following markup.

STEP-3: Add users and roles using the Web Site Administration Tool
What we have done in previous step is told ASP.NET how to authenticate users via membership, and how to authorize them using roles.
These providers have been configured, so we can now use a tool in Visual Studio that will make it easy for us to add users. From the menu bar in Visual Studio select “Website / ASP.NET Configuration” to bring up the Web Site Administration Tool.
Using the Web Site Administration Tool to Add Users
By default, your application is configured to use Windows Authentication, we need to change it to use forms authentication. So click the security tab and choose “From the internet” and save your changes.

Behind the scenes, this makes a change in web.config to set the configuration/system.web/authentication node to “Forms”, telling ASP.NET we will use Forms Based Authentication. ASP.NET will see the providers that we have configured in web.config and use them when authenticating users, adding new users, verifying roles, and other membership-related activities.
On the security tab, click the “Enable Roles” link. Then click “Create or Manage Roles”. Add a few roles, I chose “FBAAdministrators”, “FBAOwners”, and “FBAUsers”.

Click the “Create user” link to add a new user to the database. Create a user “adminuser” and assign the user to the “FBAAdministrators” role.
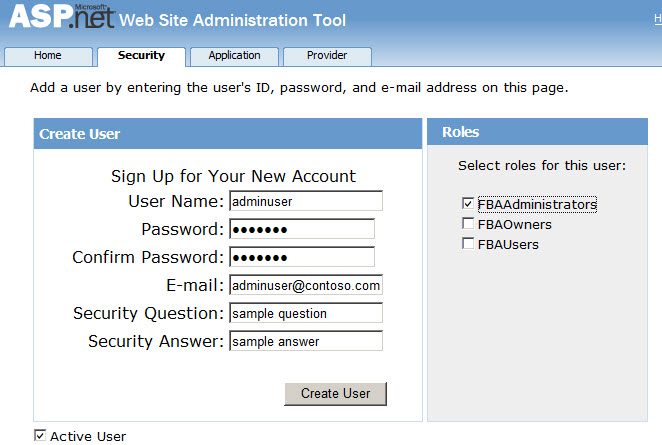
You can create other users and assign them to the various roles.
Granting Access to SQL Server
When we created the SharePoint web application, we used the Network Service account for the application pool identity. This is the account that will actually call into SQL Server for authentication and authorization. I used Network Service here for a quick example, but you probably are going to use some other service account in a real environment.
Whatever identity you chose for the application pool needs to have access to SQL Server. Add a login for SQL Server for the account used in the application pool.
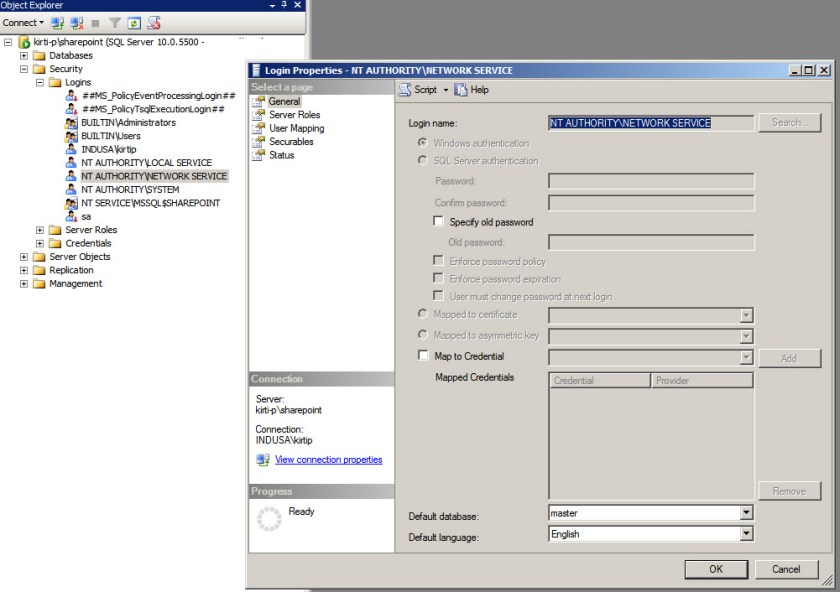
Now, grant permissions to that user by adding them to the appropriate roles.
I added the user to the aspnet_Membership_BasicAccess and aspnet_Roles_BasicAccess roles
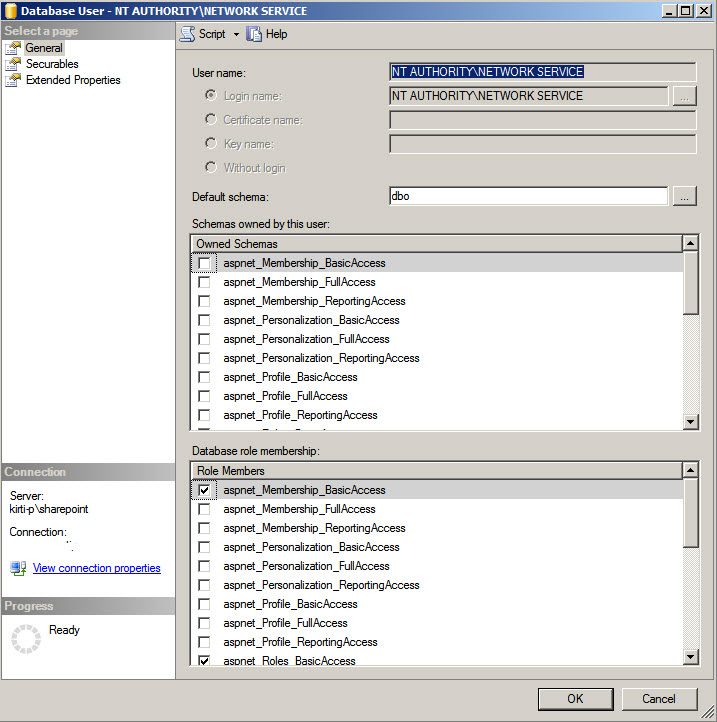
This is important so remember to do this, otherwise you will receive errors that the security token service is not activated.
STEP-4: Add connection strings in the web.config for:
Now in this step we will edit the web.config for
- Your application
- Central Administration
- Secure Token Service Application
We will add the same settings that we used above in the temporary ASP.NET application, with some slight variances. We could edit this stuff by hand, but we will show how to use the IIS Manager tool for IIS 7 to make this easier and less error-prone.
Add the Connection Strings
- Your application (11574)
Open the Internet Information Services Manager MMC snap-in. Expand the “Sites” node to reveal the web application we created (In my case it is 11574).
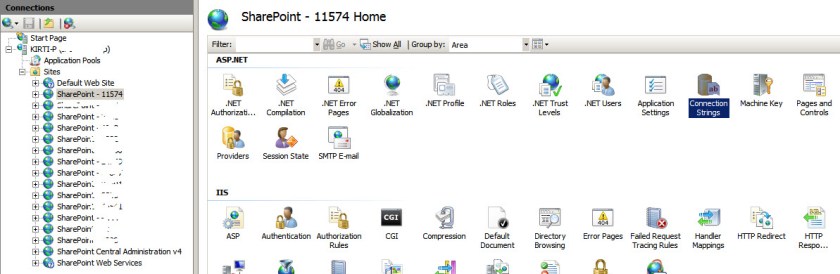
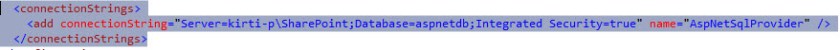
Double-click the Connection Strings feature, and under Actions choose Add. Add a new connection string called AspNetSqlProvider (this is case-sensitive) and click OK.

Behind the scenes, that created a new connection string in the following file:
C:\inetpub\wwwroot\wss\VirtualDirectories\11574\web.config
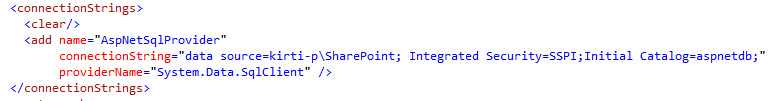
The new entry will look like this
- Central Administration
Now, click on the “SharePoint Central Administration v4” node in IIS Manager and double-click on Connection Strings and add a new connection string like we did in the previous step.
- Secure Token Service Application
Now, expand the “SharePoint Web Services” node in IIS Manager and choose the “SecurityTokenServiceApplication” node. Double-click on the connection strings feature and add a connection string just like before.
Make sure, all Web.Config have same connection string. (Please double check before going further)
STEP-5: Add membership and role providers:
- Your Application (In my case it is 11574)
In the IIS Manager, click on the “Your Application” (in my case SharePoint – 11574) node again to reveal the list of features for the web application. Double-click on the “Providers” feature.

Add a new role provider called “FBARoles”. Specify the type as “SqlRoleProvider”, the ApplicationName as “/”, and the connection string name as “AspNetSqlProvider” (available in a drop-down to reduce the likelihood of fat-fingering this).
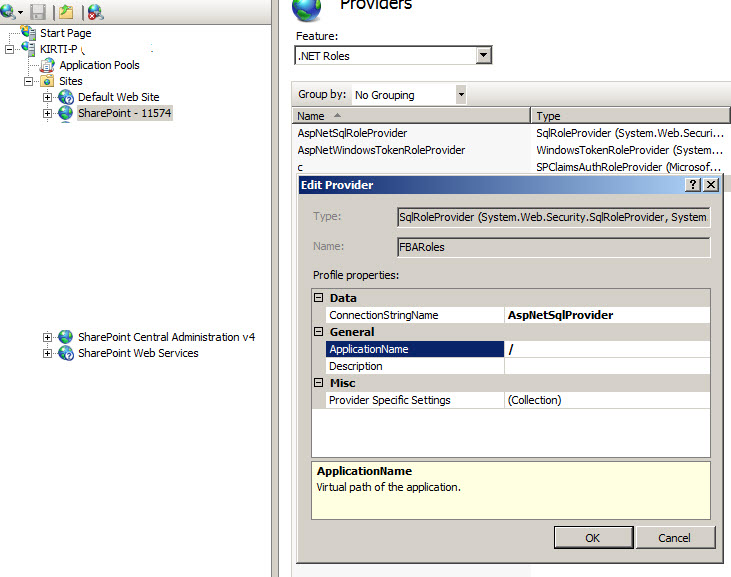
NOTE: Make sure You selected .NET Roles from feature dropdown
Add a new membership provider called “FBAMembership”. The type is SqlMembershipProvider, connection string name is “AspNetSqlProvider”, and the application name is “/”.
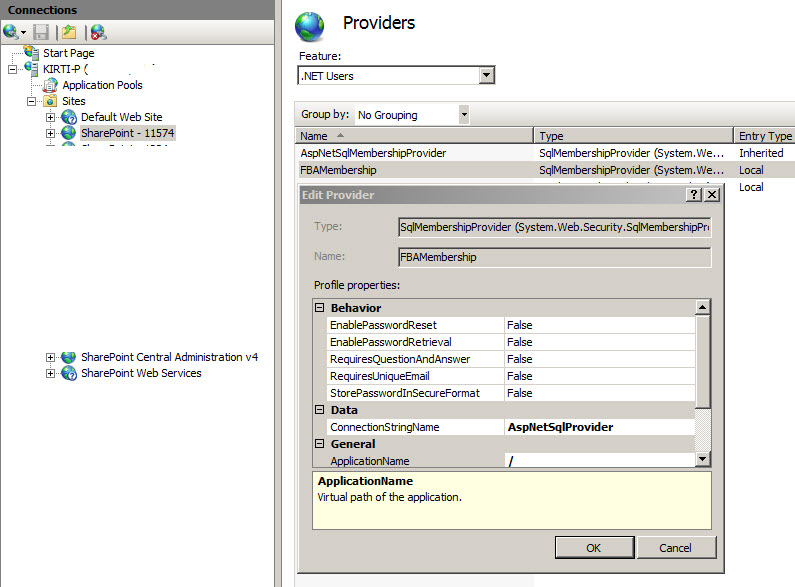
NOTE: Make sure You selected .NET Users from feature dropdown
After this, the result looks like this:
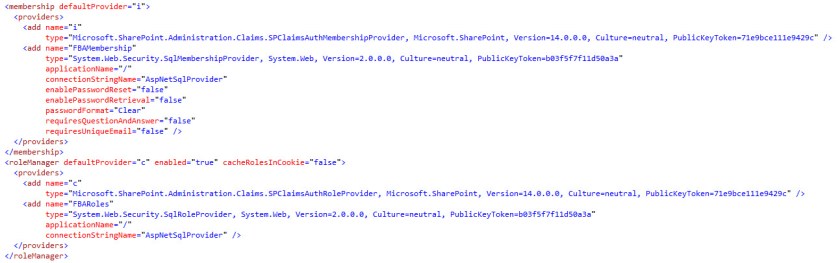
- Central Administration
Click the “SharePoint Central Administration v4” node and make the same edits to its configuration, adding the FBAMembership and FBARoles providers as described above.
- Secure Token Service Application
Expand the “SharePoint Web Services” node, select the “SecurityTokenServiceApplication” node, and add the FBAMembership and FBARoles providers.
STEP-6: Edit web.config for Central Administration
In the previous section, we added configuration for connection string, membership, and roles to our web application. We also need to add these settings for Central Administration so that we can add our forms-based authentication users as site collection owners (among other settings).
We need to make a few small twists to the configuration for Central Administration. Open central admin web.config file using MMC console and update
- The defaultProvider for the role section must be AspNetWindowsTokenRoleProvider
- The defaultProvider for the membership section must be our new membership provider, “FBAMembership”
After updating, Central Administration Web.Config looks like this after doing above changes.

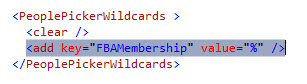
- Add the PeoplePickerWildcards entry
While we are editing the web.config for Central Administration, there’s one more thing that we need to be sure to add.
We need to enable wildcard searches for our users when using the People Picker control. This section is located under configuration/SharePoint/PeoplePickerWildcards.
STEP-7: Edit web.config for the Secure Token Service Application
Just like we did with Central Administration, we need to set the default providers for the Secure Token Service Application. Open the web.config file at:
C:\Program Files\Common Files\Microsoft Shared\Web Server Extensions\14\WebServices\SecurityToken\web.config
You will need to add your connectionStrings section and a web.config section.
It looks like as below image after adding:

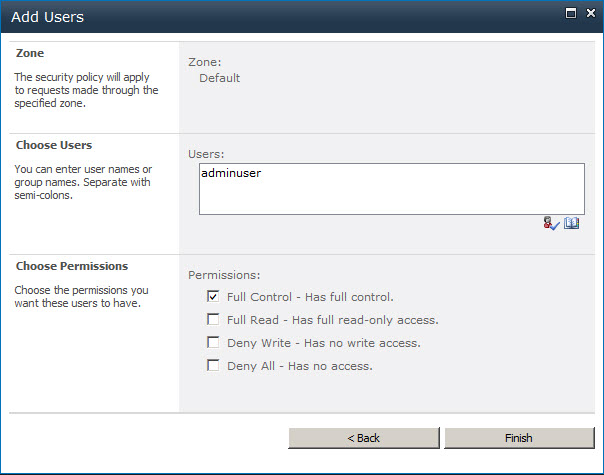
STEP-8: Add the FBA administration user to Central Administration
Open SharePoint Central Administration.
Under Application Management click “Manage web applications” and click the “Your Applicatioin” (SharePoint – 11574 in my case) item. That will light up the “User Policy” ribbon toolbar item. Click the User Policy ribbon button.

Now Click Add Users.

You are then asked what zone to configure users for, choose “Default” and click Next.
In the Choose Users section, you should be able to enter “adminuser” and the name will resolve and give full control.
The result in the policy window shows our user with the user name “i:0#.f|fbamembership|adminuser”.
Open up your new web site and Choose Forms Authentication, then sign in as adminuser.
Bingo!!! You are now logged into your site as adminuser, with site administrator privileges.
We gave the adminuser user full control of the application, now we can add other users to access this site.
STEP-9: Add FBA users to SharePoint groups
You can also add the remaining users into SharePoint site now with different access.
Thats it!!! Now try to login with different users which you added in sharepoint site.
What if you want to create your own custom login page? Read my next article “Creating a Custom Login Page for FBA in SharePoint 2010”
Nice post!
zee
http://walisystemsinc.com
Thanks buddy 🙂
Hi KP,
Very Nice post !!!
I was just looking for the same topic and I went through your post and I have done.
Very nicely written. Please keep it up and share your knowledge.
Thanks,
Chandresh
Thanks Chandresh. Lots of things will come. Keep watching 🙂
Well why doesn’t people picker identifies my administrator for FBA demo site collection??
Sunny,
Can you please check your CA site’s web.config file for below tag:
This tag should be there with your membership provider name.
Well why doesn’t people picker identifies my administrator for FBA demo site collection??